Health data breaches cost organizations an average of $10.93 million per incident, according to IBM’s 2024 report. When employee health information leaks, trust erodes and compliance violations pile up fast.
At The Pledge, we believe secure health data platforms aren’t optional anymore-they’re essential infrastructure. This guide walks you through how to protect privacy while keeping data accessible to the right people.
Why Breaches Cost More Than You Think
Healthcare data breaches reached 725 incidents in 2023, exposing over 119 million patient records according to the U.S. Department of Health and Human Services. IBM’s 2024 data breach report pegged the average cost per incident at $10.93 million, but that figure masks the real damage. When a breach hits, organizations face regulatory fines under HIPAA that can reach $1.5 million per violation category per year, plus legal settlements, forensic investigations, and the operational chaos of notifying affected patients. Anthem’s 2015 breach of 79 million records cost the company $115 million in settlement alone. Beyond the financial hit, breaches destroy employee confidence in their employer’s ability to protect their most sensitive information. Employees whose health data leaks are significantly less likely to engage with workplace wellness programs or trust digital health tools, which means your organization loses the preventative care benefits that actually lower long-term costs. The compounding effect matters: a single breach can trigger years of reputational damage and reduced employee participation in health initiatives.
Compliance Has Real Teeth Now
Regulatory frameworks have evolved from guidelines into enforceable mandates with serious consequences. HIPAA’s Security Rule requires administrative, physical, and technical safeguards for electronic protected health information, with the 2013 Omnibus Final Rule making business associates directly liable for breaches. GDPR in Europe imposes fines up to 4 percent of global annual revenue for data protection violations. POPIA in South Africa and emerging frameworks across Asia-Pacific create a fragmented but increasingly strict global landscape. Organizations can no longer treat compliance as a checkbox exercise. Regulators now expect regular risk assessments, documented security procedures, workforce training, and audit trails that prove you identified vulnerabilities and took corrective action. If a breach occurs and investigators find you skipped a required safeguard, penalties multiply.
Moving From Compliance to Control
The practical path forward requires three concrete steps. First, implement role-based access controls that limit which employees can view specific patient records. Second, automate data classification to identify sensitive information across systems (file shares, legacy databases, cloud repositories). Third, conduct annual security audits to catch gaps before regulators do. These actions transform compliance from a reactive obligation into a proactive defense. Organizations that take this approach reduce their exposure window significantly and demonstrate to regulators that they maintain a genuine security posture rather than a superficial one.
The next section explores how secure health platforms centralize data safely while maintaining these controls automatically, so your team can focus on care delivery instead of manual compliance work.
How Secure Health Platforms Centralize Data Safely
The Data Sprawl Problem
Centralized platforms eliminate the fragmentation that creates security vulnerabilities in the first place. When patient data lives across disconnected systems-EMRs, billing databases, cloud storage, mobile apps, and third-party integrations-each connection point becomes an attack surface. A 2023 Spirion analysis found 16,000 unprotected patient files scattered across 1,200 endpoints in a single healthcare organization, discovered within 48 hours. That sprawl is the real problem. Secure platforms consolidate this data into a single, hardened environment where encryption happens automatically rather than depending on individual staff members to remember security protocols.
Encryption and Access Controls
Encryption at rest and encryption in transit secure patient data using industry-standard algorithms and protect information moving between systems. More importantly, access controls based on role and job function mean a billing clerk never sees surgical notes, and a family member using the Family Share feature only accesses records the patient explicitly granted them. This minimum-necessary principle isn’t bureaucratic overhead-it’s the difference between a contained incident and a massive breach. Role-based access ensures that each team member views only the data their position requires, which reduces both risk and operational friction.
Real-Time Monitoring and Threat Detection
Real-time monitoring detects unusual access patterns immediately. If someone attempts to download 500 patient records at 3 a.m., the system flags it and alerts security teams before data leaves the platform. These systems generate complete audit trails showing exactly who accessed what data and when, which regulators now expect as proof of genuine security posture rather than superficial compliance. The audit trail becomes your strongest defense during investigations and regulatory reviews.
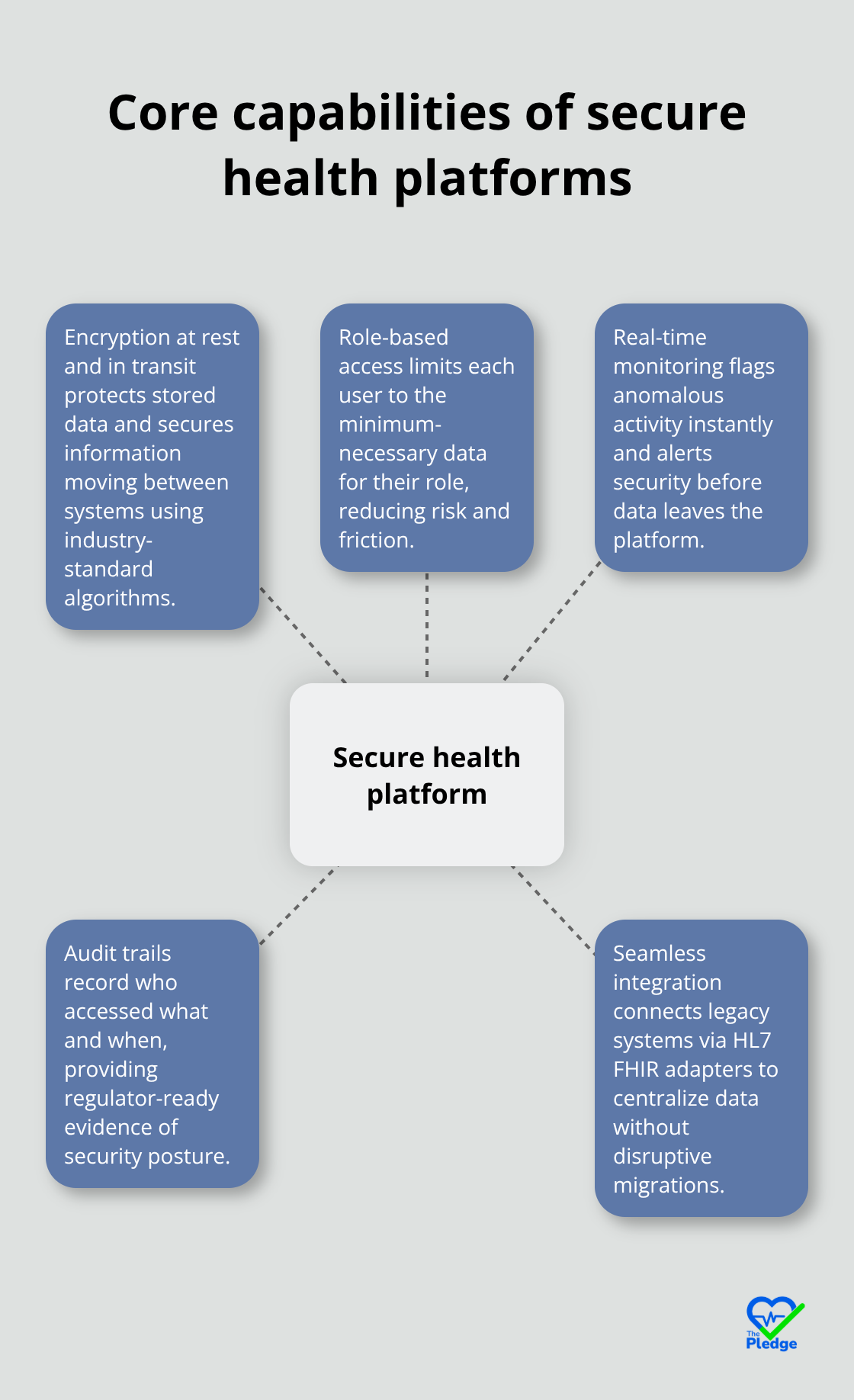
Seamless Integration Without Disruption
Integration with legacy systems happens through standardized protocols like HL7 FHIR adapters, allowing older databases to connect without forcing a disruptive rip-and-replace migration that destabilizes operations. Organizations reduce their breach response time from weeks to hours and their exposed data from thousands of records to dozens. Spirion’s analysis showed a 92 percent reduction in overexposed patient information within one month after implementing automated remediation across a healthcare network. That’s not theoretical-it’s measurable impact on actual risk. When your platform automatically classifies data according to HIPAA, GDPR, and POPIA standards, applies appropriate protections, and maintains searchable records of what happened, audits shift from nightmare scenarios to straightforward documentation exercises. Your team spends less time hunting for compliance evidence and more time delivering care.
The next section explores the specific practices that keep patient privacy intact when multiple stakeholders-providers, family members, and employers-need access to the same health information.
Controlling Access When Multiple Stakeholders Need Patient Data
Role-Based Access Prevents Unauthorized Exposure
Shared health ecosystems demand precise access boundaries. When a patient’s cardiologist, primary care physician, family member, and employer wellness coordinator all need visibility into different aspects of the same health record, the temptation is to grant broad access and hope nothing goes wrong. That approach fails consistently. The HIPAA Security Rule explicitly requires role-based access controls that limit staff to the minimum necessary information for their specific job function. A billing department employee has no legitimate reason to view surgical notes. A family member using a Family Share feature should only access records the patient explicitly authorized.
The difference between a contained incident and a catastrophic breach often comes down to whether access controls actually enforce these boundaries or exist only on paper. Organizations that implement attribute-based access control systems map specific data categories to approved roles and purposes, so a researcher studying cardiology outcomes receives access only to cardiac-related records, not psychiatric history or reproductive health information. This granularity prevents both intentional misuse and accidental exposure.
Automated Systems Replace Manual Judgment
Real-world implementation requires technical systems that automatically enforce these policies rather than relying on staff judgment. Spirion’s analysis of healthcare organizations showed that uncontrolled access across 1,200 endpoints created 16,000 unprotected patient files in a single organization. Once automated access controls were deployed based on role and clinical context, that organization achieved a 92 percent reduction in overexposed data within one month. The improvement wasn’t theoretical compliance theater-it was measurable risk elimination.
Secure Data Sharing With Explicit Consent
Secure data sharing between stakeholders demands explicit consent mechanisms and encrypted transfer protocols that create audit trails proving exactly who accessed what information and when. When a patient authorizes their cardiologist to share specific records with a surgical team, that authorization should live on an immutable record that regulators can verify. Time-bound access links that expire automatically prevent lingering exposure. Encryption during transit protects data while it moves between systems, and encryption at rest ensures that even if storage is compromised, the information remains inaccessible without proper credentials.
Continuous Auditing Catches Control Failures
Annual security audits must test these controls with actual penetration testing rather than checklist reviews. Many organizations discover during real audits that role-based access policies exist in documentation but aren’t actually enforced in their systems, or that legacy databases lack encryption capabilities entirely. Addressing these gaps before regulators find them during breach investigations saves millions in penalties and operational disruption. The most effective organizations treat security audits as continuous processes rather than annual events, using automated monitoring to detect access anomalies in real time and generate reports that prove compliance to regulators proactively rather than reactively.
Final Thoughts
Secure health data platforms deliver measurable financial returns alongside privacy protection. Organizations that implement centralized systems with automated access controls reduce breach response time from weeks to hours and cut exposed patient records by up to 92 percent within the first month. IBM’s 2024 data breach report shows the average healthcare incident costs $10.93 million, but that figure drops significantly when organizations prevent breaches through proper infrastructure rather than managing aftermath.
Moving forward with confidence in your health data requires treating security as operational infrastructure rather than compliance overhead. Real-time monitoring, role-based access controls, and automated data classification eliminate the manual judgment calls that create vulnerabilities. Your team recovers hours each week by removing manual compliance tasks, which means more focus on patient care and less time hunting for audit evidence.
Technology plays the decisive role in making this possible. Platforms designed specifically to protect patient privacy while enabling data access transform fragmented records into a unified, protected environment where you automatically enforce HIPAA, GDPR, and POPIA standards while generating audit trails that prove compliance. The Pledge centralizes health information across providers, family members, and employers while maintaining strict access boundaries and encryption standards that turn regulatory reviews into straightforward documentation exercises rather than crisis management.










